Everyone in the tech/security world knew this was coming, we just hoped we were wrong. Hackers are now holding hospitals hostage around the country.
During the past several weeks, smaller hospitals have been subject to ransomware attacks by hackers and virus writers. Ransomware attacks have been around for a long time. The idea is simple: disable a victim’s computer or data somehow, then demand payment — ransom — for its release.
“Your money or your data!” Was how we posed the problem a decade ago on the Red Tape Chronicles. Now, it really does seem like the threat is rising towards “Your money or your life.”
Ransomware attacks gained steam about two years ago when a virus named CryptoLocker infected seemingly millions of victims around the globe. The tool cleverly encrypted data and demanded payment for the key to decrypt it. ZD Net estimated that between October and December 2013, victims paid $27 million to get a key to their data. Even government agencies were hit by the virus.
Consumers are small potatoes, however, and rarely have life of death data on their PCs. Who does have life or death data? Hospitals.
As is customary these days, reporter Brian Krebs first started writing about hospital victims after Hollywood Presbyterian Hospital was hit. It reportedly paid $17,000 to regain access to its systems.
The last week, Henderson, Kentucky-based Methodist Hospital declared a “state of emergency” after falling victim to a ransomware attack.
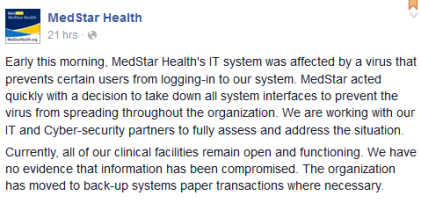
Now this week, a Washington D.C.-area chain of hospitals appears to be hit. MedStar Health put this message on its Facebook page yesterday.
“Early this morning, MedStar Health’s IT system was affected by a virus that prevents certain users from logging-in to our system. MedStar acted quickly with a decision to take down all system interfaces to prevent the virus from spreading throughout the organization. We are working with our IT and Cyber-security partners to fully assess and address the situation.”
MedStar, which operates 10 hospitals and 250 outpatient facilities, hasn’t attributed the attack as ransomware yet, the signs are there. Its systems remain down.
It’s important to note that all victim hospitals say only administrative computers are impacted. Medical care is not.
“Currently, all of our clinical facilities remain open and functioning. We have no evidence that information has been compromised. The organization has moved to back-up systems paper transactions where necessary,” MedStar says.
But you can bet a lot of doctors and nurses are swearing as they do all their tasks on paper. But so far, no one can attribute an illness or death to hacker activity. On the other hand, it’s hard to imagine a computer lockout isn’t causing serious stress inside these health care facilities, akin perhaps to a power outage.
“When it comes to medical equipment, ransomware can be exceptionally dangerous in a hospital environment,” said John Kuhn, Senior Threat Researcher, at IBM Security. “Many of these devices run Windows as the base operating system, allowing them to become susceptible to these attacks. Once malware infects a critical device, it would become completely inoperable and has the possibility to put lives at risk. With the evolution of ransomware in hospitals, it’s hopefully a wake-up call for the healthcare industry to focus on security.”
Could this be a single gang using the same trick over and over? That’s possible, raising hope that the attacks could be stopped if law enforcement tracks down the criminals. But hackers are nothing if not copycats. You can bet the success of these attacks means other gangs will imitate them.
“Ransomware exists for the same reason other viruses exist…money,” said Kevin Watson, CEO of Netsurion, a provider of remotely-managed security services for healthcare organizations. “It is designed to prey upon the unsuspecting, but rather than suck data out of a network, it cuts to the chase and asks for the cash up front. This type of malware has proven to be successful because it does an excellent job of balancing the carrot with the stick, if you will. It typically asks for a small enough amount of money to make it cheaper and easier to just pay it than to go through the time and hassle of trying to get your systems back by rebuilding your computers.

1 Trackback / Pingback